AAD / Exchange online management using AKS.
Group management is necessary to have governance and compliance in check. The main idea of any governance talk is to have Azure Policies and A
As a security-conscious person, I try all the time to find new ways to enhance my security posture in ways where I get the best of both worlds without adding too much complexity. That means that I want to have the latest and greatest security measures implemented without having a very complex infrastructure which, in the end, it might end up as a single point of failure.
In some ways, you might consider me more of a paranoid person rather than a security-conscious person. My whole home has layers over security layers implemented where you might say that I harbor military secrets.
For example, I have multiple WIFI networks with VLAN segregation, zero access to the IoT systems. IPS system on edge, logging sent to Azure Sentinel, and the list can go on.
My primary purpose in setting up this kind of security is that I fiddle with home automation, and I do not like the idea of having IoT devices roaming around the network without any control. I recommend it to all people who want to fiddle around with intelligent systems and be safe from prying eyes (tinfoil hat on).
If you’re asking yourself where I’m going with this and how it is related to this article’s title, security is a 24/7 job, and you need to be constantly aware that issues will arise one way and another.
The problem with my setup is that I have a single point of failure that revolves around identity. Everything requires a username and password with the “benefit” that they only work when you’re nearby. What happens when you start exposing things on the internet? That proximity goes away.
Many systems require that username/password model, and while there are many password managers out there, you still rely on how strong that password it is. As you’ve seen, the industry’s major push is to enable two-factor authentication, which requires a physical object to prove that you’re the owner of that account.
When you set up a new M365 account or create a new Azure subscription, you will always get a notification that you should enable two-factor authentication using the Microsoft Authenticator app.
The fun part of using the Authenticator app from Microsoft is that you even get the possibility of enabling password-less authentication, where you input the username you want to use to login and immediately receive a notification on your phone to approve the login. Zero passwords, zero headaches.
Fun right? No more passwords to remember.
So, where does FIDO2 fit in this equation? Well, the Fast Identity Online (FIDO) Alliance works diligently to remove passwords from the equation by creating open standards that can be implemented quickly and securely. FIDO2 is the latest standard in web authentication standard (WebAuth).
FIDO2 security keys enable users to log in to systems without the need for a username or password, which means that you insert a device in a USB port and press on it to log in.
Windows Hello, for example, is a FIDO2 compliant system that allows you to use your face to log in to Microsoft systems.
Seems like a fit for you? Want to know how to get started?
Let’s go then. First of all, you need either a security key, FIDO2 compliant webcam, or a laptop with Windows Hello enabled (Face, Fingerprint)
I have two Yubikeys, two eWBM GoldenGate biometric keys, and a Logitech BRIO webcam (is Windows Hello enabled) which I constantly use at home or when I’m out.
Before I got the eWBM biometric keys, I had the Yubikeys, but I couldn’t turn back to push-based keys after getting the fingerprint ones. The reality is that anybody can take your key and press on it, but if you carry with you a biometric one, they need to get your finger as well.
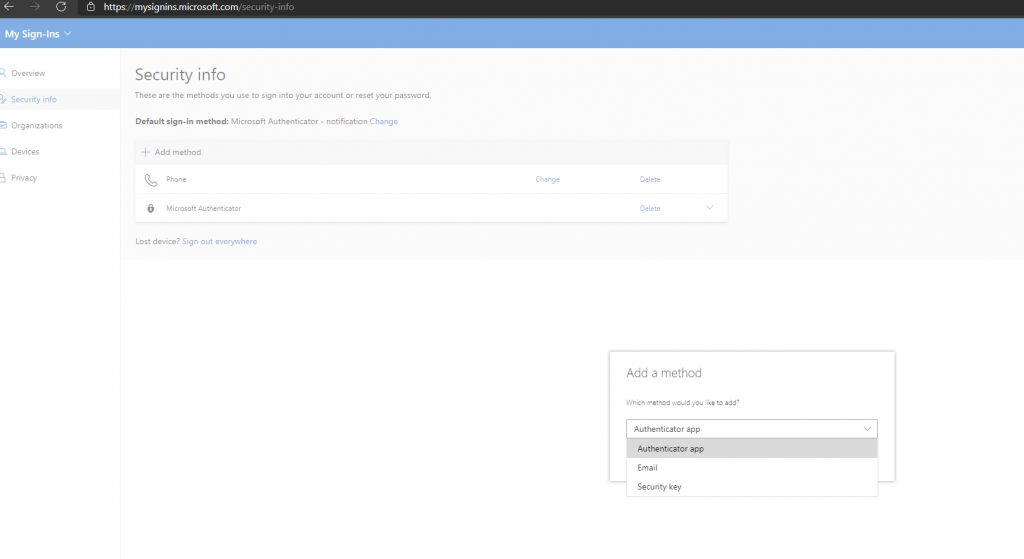
Once you get your security key or Windows Hello camera, you need to register it in your authentication provider. I, for one, use my keys to authenticate to Microsoft services, primarily Azure, so that’s the example I will give today.
The flow of registering your key is pretty straightforward if you have a personal Microsoft tenant or the required access in your organization.
First of all, you need to go to the Azure Active Directory blade in the Azure portal – Authentication methods – Microsoft Azure – and enable FIDO2 keys and combined security info for registration experience.
For FIDO2, set it as enabled for all users and the same for the experience.
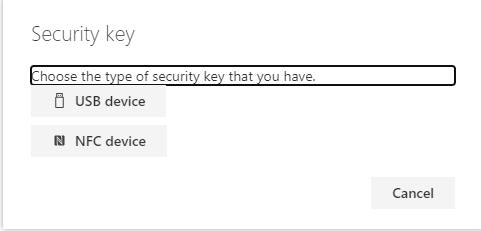
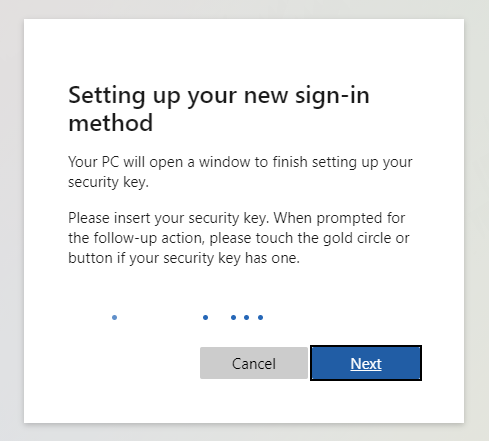
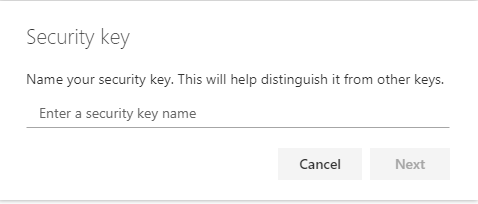
After that, go to My Sign-Ins (microsoft.com), login to your account, add a new authentication method with a security key, then follow the steps provided.
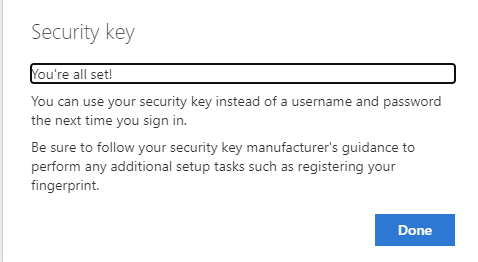
Once you’re set, then all that remains is to log in to Azure, M365, and other MS systems with your security key and enjoy not giving a damn to remember a username or password ?
As a bonus, I recorded a video of how the flow would look.
Now that we’re at the end, the security key you purchased will not only be helpful for Microsoft service. Multiple services support FIDO2 authentication, and more and more start providing services around it and for free as a bonus. I use my security keys with GitHub, Dropbox, 1Password, and the list goes on.
That being said, while you can secure your MS tenant, Azure subscription, and so on, you also can use it to secure your services with one single key and get away from the hassle of remembering passwords and so on.
When I wipe my system or laptop (force of habit of bashing them while testing edge case scenarios), I only need to have my security key and phone with me, and that’s it. All my passwords are saved in my password manager; my system deployments are done with a combination of PowerShell, Chocolatey, and GitHub; all that’s while maybe remembering one single password.
